Why intelligence is fundamental during an ECM procurement process
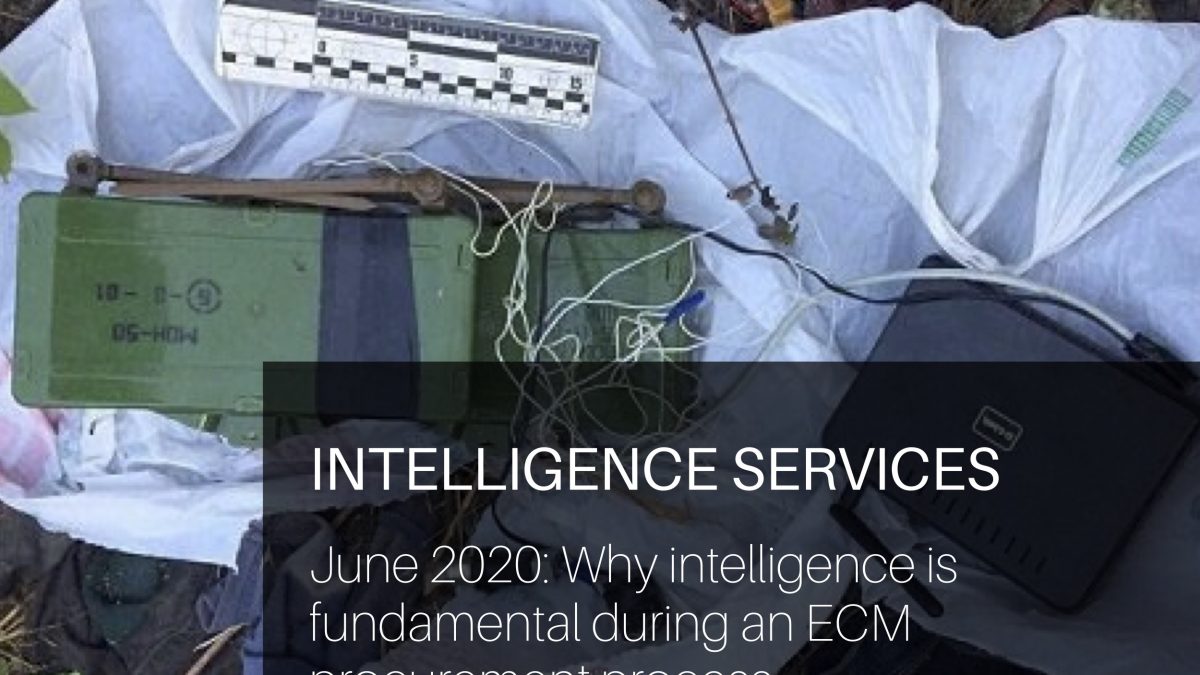
 The improvised explosive device (IED) is, and will continue to be, the most convenient weapon of choice for insurgents, terrorists and malign actors, and increasingly, criminals across the globe. IEDs are easy and cheap to produce, transport and emplace, and can cause catastrophic impacts out of all proportion to their cost and size. This makes the IED a formidable and unpredictable threat to military forces, law enforcement communities and the civilian population.
The improvised explosive device (IED) is, and will continue to be, the most convenient weapon of choice for insurgents, terrorists and malign actors, and increasingly, criminals across the globe. IEDs are easy and cheap to produce, transport and emplace, and can cause catastrophic impacts out of all proportion to their cost and size. This makes the IED a formidable and unpredictable threat to military forces, law enforcement communities and the civilian population.
As a result, military, security, justice, commercial and official organisations must ensure that the operational and technical emphases on Counter-IED (C-IED) are maintained at a level appropriate to the current or emerging threat in order to maintain supremacy over force protection and freedom of action. Horizon scanning is key.
EWS has long realised that intelligence should be guiding the ECM procurement process and the development of Mission Fill and related specialist applications. Intelligence is the foundation that the C-IED process is built on. Accurate, timely, fused information from all available sources is essential to understanding the adversary’s IED system, its networks and critical vulnerabilities, leading to more effective targeting of the IED and improvised threat network.
Successful mitigation of the threat can only be achieved if we truly understand the underlying principles of attack. Therefore, in order to maximise the effect of ECM capability, we must first understand what the current and likely future threat is or may be. An accurate understanding of the composite facets of current and future threats develops an informed judgement of risk and how we choose to manage it.
“If you know the enemy and know yourself, you need not fear the result of a hundred battles. If you know yourself but not the enemy, for every victory gained you will also suffer a defeat. If you know neither the enemy nor yourself, you will succumb in every battle.”
― Sun Tzu, The Art of War
Understanding the threat can be a challenge if the only data available is classified. A great deal of information about IED Tactics, Techniques and Procedures (TTP) can be gleaned when an informed eye is cast across the information available in open sources. Our Analysts critically monitor information available in the public domain, which allows us to see the most commonly used TTPs and devices. Trend analysis by region, device type and/or organisation is a particularly important part of understanding what is a common, new or emerging threat.
Obtaining threat data from classified sources is usually a complex and lengthy process. Exploitation takes time and is often not timely enough to meet the challenges of the intelligence customer or technology provider; often, protective marking of the data makes it inaccessible to all but a few users.
Conversely, data from the Open Source Threat Database (OSTD) is delivered in near real time, offering data which can be easily accessed by our subscribers and providing greater flexibility and speed when developing ECM equipment and Mission Fills.
As the threats we face in today’s world become increasingly complex and constantly evolve, we need to utilise every intelligence source available to us to continue to counter the threat presented by the ever-evolving tactics of state actors. Information Advantage and Information Superiority are key now and will play an even bigger part of all operations in the future, be they asymmetric or near-peer.
EWS is proud to utilise the skills and experience of its DKEs to support the development of electronic warfare capability, helping it evolve into a formidable force protection asset for our military and civilian services. Expert analysis of Publicly Accessed Information (PAI) plays a key part of this process.
Online demonstrations and trial logins are available for the OSTD. Contact Troy Phillips in the first instance to discuss your requirements.




